rauc-hawkbit-updater v1.0 Released
Back in 2018, rauc-hawkbit-updater was started by Prevas A/S as a C/GLib port of our rauc-hawkbit Python prototype (also called RAUC hawkBit Client) that was mainly developed for showcases and to serve as a demonstration and evaluation platform for others.
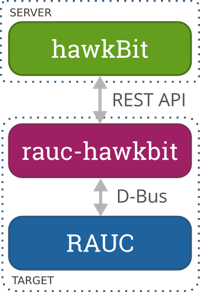
rauc-hawkbit-updater instead is explicitly developed with real-world use cases in mind. Just as its earlier Python counterpart, it operates on the target as an interface between RAUC, the embedded Linux update framework, and hawkBit, an OTA roll-out backend framework.
Since its first incarnation in 2018, rauc-hawkbit-updater's code was refactored, bugs were fixed, and features were added. With the addition of a test suite that was capable of performing interaction tests with actual hawkBit test instances, the project got more mature and, with the beginning of 2020, rauc-hawkbit-updater was finally moved to the RAUC GitHub organization under the maintenance of Lasse Klok Mikkelsen (Prevas A/S).
Now, more than a year later after more refactoring, stabilization and initial documentation, we're very happy to announce the first release version: rauc-hawkbit-updater 1.0!
Up Next
We won't stop here. A whole bunch of feature pull requests are already queued up, i.e.:
- HTTP retry handling
- Resuming interrupted downloads
- Support for action cancellation
So if you are interested in managing your embedded system's updates with RAUC and hawkBit, make sure to check it out.
Wonder How To Get Started?
- Set up a hawkBit instance (e.g. via docker)
- Set up RAUC for your target
- Cross compile rauc-hawkbit-updater for your target (a Yocto recipe for this is available in meta-rauc)
- Provide a configuration file that points to your rauc-hawkbit-updater instance
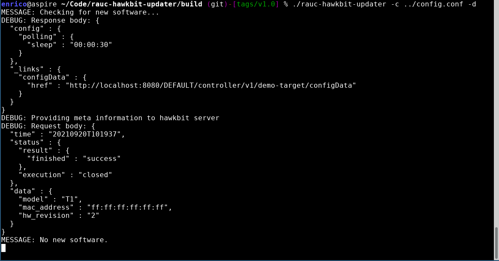
- Start the rauc-hawkbit-updater daemon on your target to let it authenticate and poll for updates
For more details follow our Quickstart guide and the documentation. You're invited to join the community, discuss and contribute! Either via matrix channel #rauc or on GitHub Issues, Pull requests or Discussions.
Finally, we would like to thank the folks from Prevas A/S for starting this project and making it open source under LGPL-2.1, and especially to Prevas' Lasse Klok Mikkelsen, the lead maintainer until the v1.0 release. Starting with v1.0, the project will now be primarily maintained by the Pengutronix developers Bastian Krause and Enrico Jörns.
Weiterführende Links
Showcase: Fail-Safe (OTA) Field Updating
Eingebettete Systeme und IoT-Geräte robust und sicher im Feld updaten zu können ist heute eine Kernanforderung jedes Produkts. Das Update-Framework RAUC ist die Basis für eine moderne und zukunftsfähige Lösung. In diesem Showcase zeigen wir die Grundprinzipien eines ausfallsicheren Update-Systems und wie Sie dieses mit Unterstützung von Pengutronix für Ihre Plattform realisieren können.
Bridging the Gap: The RAUC hawkBit Client
OTA field updates are a common requirement in modern embedded device deployments. The larger the amount of devices to control, the more important is having a good infrastructure that is reliable in updating and smart in rolling out the software.
RAUC und labgrid Sponsoring-Pakete ab jetzt im Shop!
RAUC und labgrid sind Open Source Software-Projekte, die beide bei Pengutronix gestartet wurden und in ihren jeweiligen Nischen mittlerweile recht erfolgreich geworden sind. Ab heute ist es möglich Sponsoring-Pakete im Linux Automation GmbH Shop zu erwerben, die die Entwicklung dieser Projekte unterstützen.RAUC v1.15 Released
It’s been over half a year since the RAUC v1.14 release, and in that time a number of minor and major improvements have piled up. The most notable change in v1.15 is the newly added support for explicit image types, making handling of image filename extensions way more flexible. Other highlights include improved support for A/B/C updates and several smaller quality improvements. This release also includes the final preparations for upcoming features such as multiple signer support and built-in polling.
RAUC - 10 Years of Updating 🎂
10 years ago, almost a decade before the Cyber-Resilliance-Act (CRA) enforced updates as a strict requirement for most embedded systems, Pengutronix started RAUC as a versatile platform for embedded Linux Over-The-Air (and Not-So-Over-The-Air) updates.