CERT@VDE Innovation Workshop
"Today's security challenges of embedded systems and solutions"
On June, 27th, while the sun was relentlessly heating up Germany as hardly every before, above 50 employees from many companies came together in a well air-conditioned room in the TP ConferenceCenter in Heidelberg. All operating in different fields of application but all involved in embedded systems and all interested to learn something new about security and deploying software updates.
What led them there was the CERT@VDE Innovation Workshop "Today's security challenges of embedded systems and solutions" organized in cooperation of OSADL and CERT@VDE.
What led me there was the invitation to give the audience in-depth information about how to perform fail-safe and authenticated updates on embedded devices and also present a little demo of the open source update system RAUC operating on a Raspberry Pi.
But first of all, the day started with a warm welcome from Carsten Emde, head of OSADL, and a short but quite interesting introduction round where each member shortly introduced themselves, their company and their motivation for attending. The motivation description varied from very enthusiastic statement of what was expected from this workshop or how their company is moving towards connected devices up to a simple 'what he said' in case of multiple attendees per company.
The topics of the following talks were quite diverse and covered many aspects of security.
Andreas Harner from CERT@VDE described what a CERT (short for 'Computer Emergency Response Team') actually is, what they care for and how to benefit from this. He also presented some entertaining war stories.
The next presentation was by Tim Hemel. Based on the example of an update system he pointed out different use case analysis and thread modeling techniques on different abstraction levels to find parts of specification that were not covered yet, as well as potential risks. He also noted the importance of explicitly deciding whether to address a known potential attack method because of risk vs. cost trade-off considerations.
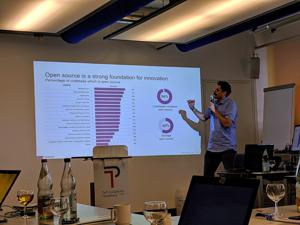
The first block before lunch was then rounded out by a talk held by Synopsis (which recently bought Black Duck) employee Boris Cipot who described himself as actually being a comedian that somehow turned into a software developer. In his vivid presentation style he gave some impressive insights about how much open source software is actually used in modern projects and products and finally touched the topic of code scanning.
After the lunch break, where we all had the chance to replenish our energy reserves with tasty food and deserts, Anne Borcherding from the Fraunhofer IOSB cared for the knowledge input again. As a 'real security researcher' as she titled herself, she introduced the different analysis techniques they use for finding vulnerabilities in code and protocols, such as black box testing, or fuzzing. With a study where they attacked 6 Profinet bus couplers from different manufacturers, she showed some real-world statistics about vulnerabilities of devices out in the field.
To also cover the legal site of security, Dr. Dennis-Kenji Kipker, Legal Advisor at CERT@VDE, gave a quick overview over the planned German IT law (2.0) and how the ministry of the interior could declare IT products as infrastructure-critical in the future to require special security-related processes and know-how. He also noted their plans to introduce a volunteer 'cyber-approved' mark for digital products...
This was the right time to move back to some more technical presentation and for me the sign to start with my talk about fail-safe and secure update systems. The ability to safely deploy updates in the field is a key requirement for fixing bugs in the field and thus for reacting on CVE's etc. I first made a quick rush through the basic concepts of redundancy, atomicity and verification to then emphasize the importance of using open source update frameworks. After a short overview over tools like mender, swupdate and RAUC, I used RAUC as an example to give a slightly more in-depth view of what an update framework provides and how to handle the requirements of robustness and security.
The coffee break gave the others the time to take a deep breath from the load of information received up to now (and taste the great cakes!) and gave Carsten Emde and me the time required to set up our demos.
After the break, I first showed the practical usage of RAUC and how to handle certificates, signing, etc. on the command line of a Raspberry PI. Then Carsten showed the bootstrapping process of mender server and how to actually update a Raspberry PI after having set up everything correctly. The demos showed the wide range between the full all-in-one solution of mender on one side and the highly configurable and adaptable client-only solution like RAUC on the other side.
The workshop track was then completed by Markus Hölscher from HENSOLDT Cyber GmbH who presented their formally verified micro kernel.
I would like to say many thanks to Carsten Emde and the entire team from OSADL for organizing this great workshop, and thanks for the little present I got. :)
As all other participants I received a certificate of participation in this workshop and then finally headed back towards home.
Further Readings
Girls' Day 2026
Unter dem Motto "Open Source - Open Future!" waren im Rahmen des Girls' Day am 23. April 2026 vier junge Frauen bei Pengutronix zu Gast. Zu Beginn gab es eine kurze Vorstellung von Pengutronix und natürlich die Antwort auf die Frage, was eigentlich dieses Embedded ist.
Pengutronix auf der embedded world 2026
Meet us at the embedded world 2026 in Nuremberg. Like every year you'll find us in hall 4, booth 4-261. As usual, we will be showing demonstrators on current topics at our exhibition stand. In addition, we are again inviting you to the RAUC and Labgrid community meetup.
You can buy RAUC and labgrid sponsor packages now
RAUC and labgrid are open source software projects started at Pengutronix, that are quite successful in their respective niche. Starting today you can buy sponsorship packages for both projects in the Linux Automation GmbH web shop, to support their maintenance and development.RAUC v1.15 Released
It’s been over half a year since the RAUC v1.14 release, and in that time a number of minor and major improvements have piled up. The most notable change in v1.15 is the newly added support for explicit image types, making handling of image filename extensions way more flexible. Other highlights include improved support for A/B/C updates and several smaller quality improvements. This release also includes the final preparations for upcoming features such as multiple signer support and built-in polling.
Pengutronix at SPS in Nuremberg
After some years of absence, Pengutronix is back at the SPS 2025 in Nuremberg. You will find us in hall 6, booth 6-350C. We are looking forward to connecting with old and new friends, partners and customers. As usual, we will be showcasing demonstrators on current topics at our exhibition stand.
RAUC - 10 Years of Updating 🎂
10 years ago, almost a decade before the Cyber-Resilliance-Act (CRA) enforced updates as a strict requirement for most embedded systems, Pengutronix started RAUC as a versatile platform for embedded Linux Over-The-Air (and Not-So-Over-The-Air) updates.
OSADL Networking Day 2017
In the last talk before lunch, my colleague Enrico Jörns talked about the RAUC (Robust Auto Update Controller) framework.