Articles with tag "rauc"
You can buy RAUC and labgrid sponsor packages now
RAUC and labgrid are open source software projects started at Pengutronix, that are quite successful in their respective niche. Starting today you can buy sponsorship packages for both projects in the Linux Automation GmbH web shop, to support their maintenance and development.RAUC v1.15 Released
It’s been over half a year since the RAUC v1.14 release, and in that time a number of minor and major improvements have piled up. The most notable change in v1.15 is the newly added support for explicit image types, making handling of image filename extensions way more flexible. Other highlights include improved support for A/B/C updates and several smaller quality improvements. This release also includes the final preparations for upcoming features such as multiple signer support and built-in polling.
RAUC - 10 Years of Updating 🎂
10 years ago, almost a decade before the Cyber-Resilliance-Act (CRA) enforced updates as a strict requirement for most embedded systems, Pengutronix started RAUC as a versatile platform for embedded Linux Over-The-Air (and Not-So-Over-The-Air) updates.
RAUC v1.14 Released
A week ago, we released RAUC version 1.14. This release — already the second in 2025 — adds support for ComposeFS artifacts, enhances the adaptive update experience, introduces new options for fallback prevention, and lays the groundwork for future features like polling-based update checks.
RAUC v1.13 Released
After several releases with smaller, more subtle changes, the v1.13 release marks a significant milestone for RAUC by introducing the initial version of the long-awaited artifact updates feature. The initial concept was created more than two years ago. In addition to this major feature, the release reflects extensive work on testing, stabilization, and a notable increase in community contributions.
RAUC v1.12 Released
With 93 pull requests that brought in 248 new commits, a lot happened since the last release on master (v1.11.1). The new v1.12 version of RAUC focusses on making it even more robust while adding some features and improvements.
RAUC v1.11 Released
Ho Ho ho! As the year's progress bar approaches 99%, another update is already completed: RAUC v1.11 is here!
RAUC v1.10 Released
Just in time for the EOSS 2023 in Prague, we have released v1.10 of RAUC. Just-in-time means the release was actually finalized by Jan Lübbe in the train to Prague (like I finally wrote the majority of this blog post on the train back).
RAUC v1.9 Released
"Getting things off the ground" could be the motto for the v1.9 release of RAUC. The support for custom metadata in the manifest got a step further, a new, more flexible, D-Bus API for bundle inspection paved the way for obtaining more detailed information, and a new manifest hash marks the first of several planned changes for configurable event logging. However, one of the most invasive changes happened under the hood: We have started the transition from autotools to meson as a build system.
Saving Download Bandwidth with RAUC Adaptive Updates
Based on RAUC's HTTP(S) streaming capabilities, adaptive updates are a generic concept in RAUC to allow saving download bandwidth and form an alternative to conventional delta updates. This post introduces both the generic concept as well the first implemented method 'block-hash-index'.RAUC v1.8 Released
When September ends and summer is over, it's a good opportunity to take advantage of the shorter days and comfortably update to the latest RAUC version we have just released into the wild: v1.8
RAUC v1.7 Released
Better late than never: Finally, here is our blog post for RAUC v1.7, which was released a month ago.
Pengutronix at Embedded World 2022
Welcome to our booth at the Embedded World 2022 in Nürnberg!
Tutorial: Start With RAUC Bundle Encryption Using meta-rauc
In its current master branch, RAUC now supports encrypted Bundles. This tutorial will introduce you to the basics of using encryption in RAUC and show how to use it in a simplified Yocto setup with the meta-rauc Layer.
RAUC v1.6 Released
While major changes are about to come, the RAUC v1.6 release already paves the way under the hood. Built-in streaming support will be one of the next features built on top of the 'verity' bundle format in RAUC.
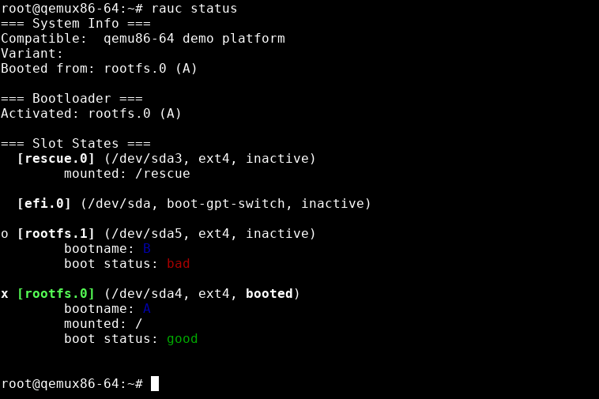
Tutorial: Evaluating RAUC on QEMU - A Quick Setup With Yocto
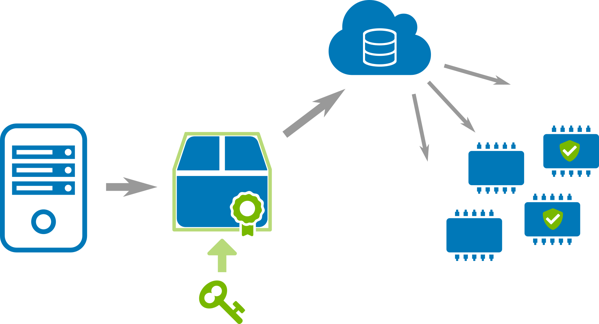
RAUC is an update framework for safely deploying verified updates on your embedded Linux devices. It ensures atomicity of the update process to protect from sudden power outages, hardware failures, etc. So, why would one like to run RAUC on an emulated platform?
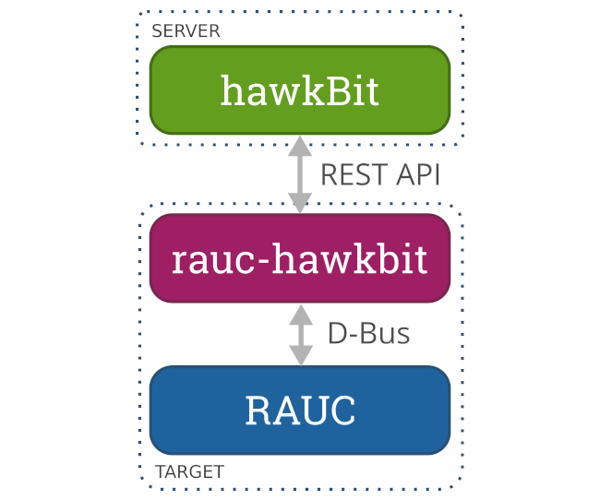
rauc-hawkbit-updater v1.0 Released
Back in 2018, rauc-hawkbit-updater was started by Prevas A/S as a C/GLib port of our rauc-hawkbit Python prototype (also called RAUC hawkBit Client) that was mainly developed for showcases and to serve as a demonstration and evaluation platform for others.
Showcase: Fail-Safe (OTA) Field Updating
Being able to robustly and securely update embedded systems and IoT devices in the field is a key requirement of every product today. The update framework RAUC is the basis for a modern and future-proof solution. In this showcase we present the basic principles of a fail-safe update system and how Pengutronix can support you with implement this for your platform.
RAUC v1.5 Released
This release fixes a vulnerability in RAUC that can be exploited under certain circumstances to achieve a local privilege escalation. It provides both a mitigation for the vulnerability when using the existing bundle format as well as a new bundle format that uses dm-verity to continuously authenticate the update data while it is installed.
RAUC v1.4 Released
It's been 3 weeks ago now since the tag for RAUC 1.4 was created. But it is vacation time and so we have a good excuse for communicating things with some delay. Fortunately, the media team is back now and so also those of you who haven't noticed the new release yet will be informed about notable changes.
RAUC v1.3 Released
Here it is, commit number 1700, 291 commits after the v1.2 tag: The v1.3 release of RAUC is out in the wild and adds a lot of new and useful features together with some fixes.
Pengutronix at Embedded World 2020
Yesterday, Embedded World started, in normal times one of the largest trade shows for embedded development in Europe. While many exhibitors (and thus maybe also lots of visitors) have canceled their presence due to the coronavirus, we present our booth and our demo show cases as usual.
RAUC v1.2 Released
Right before the ELC-E starts tomorrow, we used the time in the hotel to bake a brand new RAUC release for you (and your embedded devices)! Well, here it is: RAUC v1.2
Safe and Secure Field Updates of Embedded Linux Systems
In this blog post I would like to address the challenges of performing unattended and verified updates of embedded Linux systems in the field using open source software and workflows. While updating is not a end in itself, a second part of my considerations goes even further and also works out the necessities and possible workflows for keeping the software stack of a project up to date and thus either preventing security issues or at least enabling a short reaction time in case of severe CVE'S discovered.
CERT@VDE Innovation Workshop
On June, 27th, while the sun was relentlessly heating up Germany as hardly every before, above 50 employees from many companies came together in a well air-conditioned room in the TP ConferenceCenter in Heidelberg. All operating in different fields of application but all involved in embedded systems and all interested to learn something new about security and deploying software updates.RAUC v1.1 Released
Just before the beautiful shine of the new has fully disappeared from RAUC 1.0, it is now time to bring out a new release: v1.1.
RAUC v1.0 Released
Four days before Christmas Pengutronix prepared a very special present that probably many of you have been waiting for: The 1.0 version of RAUC!
Pengutronix at FrOSCon 2018
This year, a team from Pengutronix attended FrOSCon in St. Augustin for the first time. We took the opportunity to shake hands, talk about our latest developments and meet hackers interested in working with embedded Linux.
RAUC v0.4 Released
The RAUC team is proud to announce that we've just released RAUC v0.4!
Pengutronix at FOSDEM 2018
As in the previous years a bunch of Pengutronix developers attended the FOSDEM Open Source conference in Brussels to stay up-to-date with the latest developments in the context of embedded Linux, graphics and media, electronics and lots of other interesting topics.
RAUC v0.3 Released
The RAUC team is proud to announce that we've just released RAUC v0.3! Again, we have worked a lot on stability and support for more and more use cases. RAUC now supports pure UEFI-based booting on x86, multiple board variants in the same bundle, intermediate certificates and enhanced feedback from the boot selection layer.
Bridging the Gap: The RAUC hawkBit Client
OTA field updates are a common requirement in modern embedded device deployments. The larger the amount of devices to control, the more important is having a good infrastructure that is reliable in updating and smart in rolling out the software.
RAUC v0.2 Released
We proudly just sent out a new release of the RAUC update framework.
Comprehensive RAUC Documentation Update
As in many projects, also in RAUC phases of extensive development did often not leave sufficient time to explain the latest changes, new features or at least some basic concepts in an appropriate manner.
OSADL Networking Day 2017
In the last talk before lunch, my colleague Enrico Jörns talked about the RAUC (Robust Auto Update Controller) framework.
RAUC v0.1.1 released
RAUC is making progress, and my colleagues Enrico Jörns and Jan Lübbe finally pushed out a new release today that reflects what happened during the last months. Updating embedded linux systems in the field in a secure and robust way becomes more and more important; we had many interesting talks with our customers during the last time, and some of the new ideas are already finding their way into the codebase. However, there is still a lot of work ahead, and if you have more ideas, either drop us a note on the community channels, send patches or github pull requests, or ask for commercial help!
Chemnitz Linux Days 2017
In the first talk today, Michael Tretter reports about the current state of Open Source Graphics for Embedded Systems. For regular observers, it's probably not surprising that the focus will be on i.MX6, Etnaviv and the IPU.