Artikel mit dem Tag "security"
Wir haben doch etwas zu verbergen: Schlüssel mit OP-TEE verschlüsseln
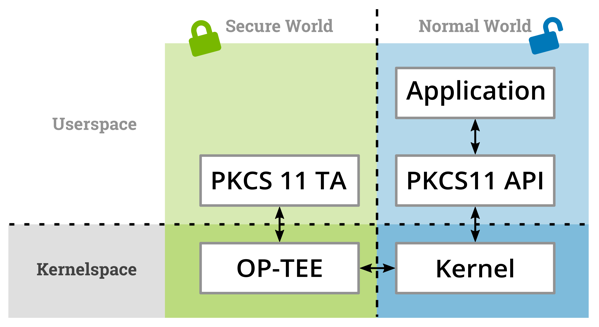
Moderne Linux Systeme müssen häufig zwecks Authentifizierung bei einer Cloud- basierten Infrastruktur oder einer On-Premise Maschine eigene kryptografische Schlüssel speichern. Statt der Verwendung eines Trusted Platform Modules (TPM), bieten moderne ARM Prozessoren die TrustZone-Technologie an, auf deren Basis ebenfalls Schlüssel oder andere Geheimnisse gespeichert werden können. Dieses Paper zeigt die Nutzung des Open Portable Trusted Execution Environments (OP- TEE) mit der Standardkonformen PKCS#11 Schnittstellen und i.MX6 Prozessoren von NXP als Beispiel.
Smart City - vom Rapid Prototyping bis zur Tragfähigen Infrastruktur
Wir wollen zum Bundesweiten Digitaltag am 18.6.2021 das Thema "Smarte Städte" ein bisschen von der technischen Seite beleuchten, aber keine Angst: es bleibt für alle verständlich.
Using OP-TEE to Authenticate IoT Devices
Deploying IoT devices into the field poses the question of how to authenticate these devices against your own services. While software authentication of bootloader, kernel, and filesystems ensures that only trusted software is run on the device, preventing extraction of authentication data from the device requires the use of a Trusted Platform Module (TPM) or equivalent mechanisms. This blog post introduces OP-TEE and PKCS#11 as a software alternative.